Terraform
Basic Interview Q&A
1. What is Terraform, and why is it used in the context of infrastructure automation?
Terraform is an open-source infrastructure as code (IaC) tool developed by HashiCorp. It allows you to define and manage your infrastructure declaratively using a simple and human-readable configuration language.
Terraform is used for infrastructure automation to provision and manage resources across various cloud providers and on-premises environments in a consistent and reproducible manner.
2. Explain the difference between declarative and imperative approaches in infrastructure provisioning.
In declarative provisioning, you define the desired end state of your infrastructure without specifying the exact steps to reach that state. Terraform follows a declarative approach, where you describe the desired infrastructure configuration, and it automatically determines the necessary actions to create or modify resources.
In contrast, the imperative approach involves specifying explicit instructions or commands to perform each step of infrastructure provisioning. Examples of imperative tools include shell scripts or configuration management tools like Ansible or Chef.
3. How does Terraform ensure the idempotency of resource provisioning?
Terraform ensures idempotency by maintaining a state file that keeps track of the resources it manages. When you run Terraform apply, Terraform compares the desired state described in the configuration with the current state recorded in the state file.
It then determines the necessary actions to reach the desired state and applies only the required changes to achieve that state. This approach allows Terraform to converge the infrastructure to the desired state regardless of the number of times you run Terraform.
4. What are the main advantages of using Terraform over traditional infrastructure provisioning methods?
Some advantages of using Terraform over traditional methods are:
Infrastructure as code: Terraform allows you to define your infrastructure in code, enabling version control, collaboration, and repeatability.
Automation and reproducibility: Terraform automates the provisioning process, making it repeatable and consistent across environments.
Cloud-agnostic: Terraform supports multiple cloud providers, allowing you to manage infrastructure using a single tool regardless of the underlying cloud technology.
State management: Terraform tracks the state of managed resources, enabling it to make precise changes and perform updates intelligently.
Scalability: Terraform can manage large and complex infrastructures, handle dependencies, and orchestrate resource provisioning efficiently.
5. What is the Terraform state file, and why is it important?
The Terraform state file is a JSON or binary file that stores the current state of the managed infrastructure. It records resource metadata, dependencies, and other relevant information. The state file is critical for Terraform's operation as it allows the tool to understand the existing infrastructure and track changes over time.
It helps Terraform determine the delta between the desired state and the actual state during subsequent runs, enabling it to apply the necessary updates accurately.
6. Describe the lifecycle of a Terraform resource.
The lifecycle of a Terraform resource consists of four stages:
Creation: When you define a resource in the Terraform configuration and run Terraform apply, Terraform creates the resource by making API calls to the provider.
Update: If you modify the resource configuration, Terraform detects the changes during the next Terraform application. It determines the necessary updates and applies them to the existing resource, ensuring it matches the desired state.
Read: During the Terraform plan or Terraform apply commands, Terraform reads the current state from the state file and the provider to understand the existing infrastructure and compare it with the desired state.
Deletion: If you remove a resource from the Terraform configuration and run Terraform apply, Terraform identifies the resource as no longer desired and proceeds to delete it from the infrastructure by making API calls to the provider.
7. How can you specify dependencies between resources in Terraform?
In Terraform, you can specify dependencies between resources using the depends_on attribute within resource blocks. By including this attribute, you define an explicit ordering of resource creation and ensure that one resource is created before another. This helps manage dependencies when one resource relies on the existence or configuration of another resource.
8. What is the purpose of the Terraform plan command?
The Terraform plan command is used to create an execution plan that shows the changes Terraform will apply to the infrastructure. It compares the desired state defined in the configuration with the current state recorded in the state file.
The plan command provides a summary of the actions Terraform will take, such as creating, modifying, or deleting resources. It allows you to review and verify the changes before applying them to the infrastructure.
9. What are Terraform variables, and how can you use them in your infrastructure code?
Terraform variables allow you to parameterize your infrastructure code and make it more reusable and configurable. Variables can be defined in Terraform configuration files or separate variable files. You can use variables to customize resource configurations, such as specifying the number of instances or setting environment-specific values.
By leveraging variables, you can avoid hardcoding values and easily reuse and share your infrastructure code across different environments.
10. How does Terraform handle secrets and sensitive data?
Terraform provides mechanisms to handle secrets and sensitive data securely. One approach is to use environment variables or input variables to pass sensitive values at runtime, ensuring they are not stored in plain text in the configuration files or state.
Another option is to use external secret management systems, such as HashiCorp Vault, to retrieve sensitive data during the Terraform execution. These practices help keep secrets separate from the infrastructure code and enhance security.
11. What are Terraform backends, and how do they help in state management?
Terraform backends are components responsible for storing and retrieving the Terraform state. They provide a persistent and centralized storage location for the state file, enabling collaboration and state sharing among team members.
Backends can store the state remotely, allowing concurrent access and locking to prevent conflicts. By using backends, you can avoid local state file storage and ensure the consistency and durability of the Terraform state.
12. Explain the difference between Terraform's local and remote backends.
Terraform's local backend is the default backend and stores the state file on the local disk. It is suitable for solo development or situations where remote collaboration is not required. The local backend does not support state locking, making it prone to conflicts in team environments.
On the other hand, Terraform's remote backends store the state file remotely, enabling collaboration and concurrent access. Remote backends offer features like state locking, versioning, and additional security controls.
Examples of remote backends include Amazon S3, Azure Blob Storage, or HashiCorp Terraform Cloud. Using remote backends is recommended for team-based workflows to ensure consistency and avoid conflicts when multiple team members work on the same infrastructure.
13. How does Terraform handle dependencies between modules?
Terraform handles dependencies between modules through the use of input and output variables. Modules can define input variables that represent dependencies required from the calling module. The calling module provides these values as arguments when calling the module.
Additionally, modules can define output variables to expose specific values to the calling module. This mechanism allows Terraform to establish a clear relationship and pass data between modules, enabling them to work together while maintaining modularity.
14. What is the purpose of the "Terraform init" command?
The "Terraform init" command initializes a Terraform working directory. It downloads and installs the necessary provider plugins, sets up the backend configuration, and prepares the directory for Terraform operations.
15. How can you import existing infrastructure into Terraform?
Infrastructure can be imported into Terraform by using the import command. This command associates an existing resource to a defined resource in Terraform configuration. This can help in managing resources that were not initially created with Terraform, or in adopting Terraform for pre-existing infrastructure.
Here is an example of its syntax:
terraform import [options] ADDR ID
- ADDR is the address of the Terraform resource to associate with the existing resource.
- ID is a resource-specific identifier to select the exact resource to import.
16. Explain the concept of Terraform workspaces and when to use them.
Terraform workspaces provide a way to manage multiple instances of a Terraform configuration. Workspaces allow you to have separate sets of resources for different environments, such as development, staging, and production. They help in maintaining isolated environments and managing the state of each workspace.
17. How does Terraform handle variable interpolation in strings?
Terraform allows variable interpolation in strings using the "${var.NAME}" syntax. When the configuration is processed, Terraform replaces the variable references with their corresponding values.
18. What are provider plugins in Terraform, and how do they work?
Provider plugins in Terraform are responsible for managing the resources of a specific cloud or infrastructure platform. They translate Terraform configurations into API calls to create, update, and delete resources.
Provider plugins are distributed separately and are automatically installed and managed by Terraform when initializing a configuration.
19. Describe how you can use Terraform to provision resources in different cloud providers simultaneously.
To provision resources in different cloud providers simultaneously, you can define multiple provider blocks in your Terraform configuration. Each provider block specifies the provider plugin and its configuration specific to the cloud provider being used. Terraform will manage resources across all defined providers during the execution.
20. How can you leverage Terraform's "count" and "for_each" features for resource iteration?
You can use the "count" and "for_each" features in resource blocks to iterate and create multiple instances of a resource. "count" allows you to create a fixed number of resource instances, while "for_each" allows you to create instances based on a map or set of values
21. What is Terraform's "force-unlock" command used for?
Terraform's force-unlock command is commonly used in situations where the automatic locking mechanism fails to unlock due to system crashes or unexpected termination of Terraform commands. It manually unlocks the state for a particular workspace.
When you run commands such as terraform apply or terraform plan, Terraform locks your state files to prevent conflicts and inconsistency caused by concurrent writes. These locks help protect your infrastructure by preventing simultaneous modifications.
However, in some cases, you may need to manually unlock the state file using the force-unlock command. This situation could arise if a Terraform command is prematurely terminated and does not have the chance to unlock the state file.
The syntax for the command is:
terraform force-unlock LOCK_ID [DIR]
- LOCK_ID is the lock ID (a unique identifier), which Terraform gives you when the locking operation goes wrong.
- DIR sets the path to your Terraform directory. If you don't set this, the command defaults to the current directory.
22. Explain how to use the Terraform "output" block for exporting resource information.
The output block in Terraform is used to define values that will be highlighted to the user upon terraform apply, or can be easily queried by the terraform output command. This can be really useful for exporting key resource information, such as IP addresses, hostnames, and other attributes for the resources created by a Terraform configuration.
Here's an example of how to declare an output block:
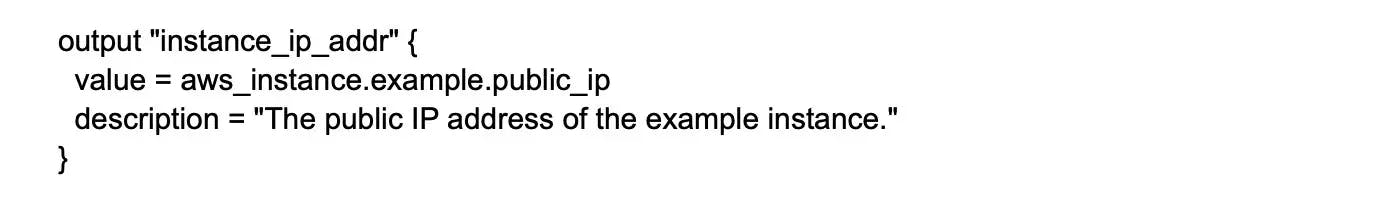
In this example, instance_ip_addr is the name of the output, while the value attribute corresponds to the public IP address of the resource named example of type aws_instance. The description attribute is optional and provides information about the output.
After applying your configuration with terraform apply, Terraform will display this output:

23. How can you handle resource dependencies between multiple Terraform configurations?
To handle resource dependencies between multiple Terraform configurations, you can use Terraform's "data" block to reference resources from other configurations. By using the "data" block, you can import values or information from other configurations and use them in your current configuration to establish dependencies.
24. Describe the purpose of Terraform's "version" constraints in module declarations.
The "version" constraints in module declarations specify the acceptable versions of a module to be used. They help ensure that the configuration is compatible with a specific version of the module and prevent unexpected changes or incompatibilities when updating the module.
25. What is the difference between Terraform's "destroy" and "refresh" commands?
Terraform's destroy and refresh commands are part of its suite of commands, but they serve vastly different purposes related to the lifecycle management of resources.
The destroy command is used to destroy or delete the Terraform-managed infrastructure. It is the opposite of terraform apply. Where the apply command creates or modifies infrastructure to match your configuration, destroy de-provisions all resources that the current Terraform configuration is managing.
On the other hand, the refresh command is used to reconcile the state Terraform has recorded with the real-world infrastructure. It does this by querying the provider to get the current status of resources.
26. How can you define multiple providers for different regions within the same configuration file?
To define multiple providers for different regions within the same configuration file, you can use provider aliases. Provider aliases allow you to access different providers based on their configurations, such as specifying different regions or authentication details. These aliases can then be referenced in resource blocks to associate them with the desired provider.
27. Explain the benefits of using the Terraform "plan" command for infrastructure changes.
The "Terraform plan" command provides a preview of the changes that will be applied to the infrastructure. It shows the actions Terraform will take, such as creating, modifying, or deleting resources, based on the current state and the proposed changes.
This helps in understanding the impact of changes before actually applying them, enabling better review and validation of the planned modifications.
28. Describe the process of using Terraform's "remote state data" feature for cross-configuration communication.
Terraform's "remote state data" feature allows you to retrieve information from another Terraform configuration's state file. By referencing the remote state, you can access and use values from other configurations, facilitating communication and coordination between different Terraform-managed resources.
29. How can you use the "depends_on" attribute in Terraform resource blocks?
The "depends_on" attribute in Terraform resource blocks defines an explicit dependency between resources. It ensures that the resource with the "depends_on" attribute is created or modified before the dependent resources, regardless of any implicit ordering. This attribute is useful when there are dependencies that Terraform cannot automatically detect.
30. What is the purpose of the Terraform "import" command?
The "Terraform import" command is used to import existing resources into the Terraform state. It allows Terraform to manage and track existing resources that were not initially created using Terraform, enabling their inclusion in the Terraform configuration and state management.
31. How can you use Terraform to manage infrastructure across multiple cloud providers simultaneously?
Terraform supports managing infrastructure across multiple cloud providers by utilizing provider plugins specific to each provider. By defining provider blocks and their configurations for each cloud provider, Terraform can orchestrate the provisioning and management of resources across multiple providers in a single configuration.
32. What is the purpose of the "Terraform refresh" command, and when would you use it?
The "Terraform refresh" command retrieves the current state of the infrastructure resources and updates the Terraform state file to match the real-world resources. It is useful when changes have been made outside of Terraform's control and the state file needs to be updated to accurately reflect the actual state of the infrastructure.
33. Describe how you can use the "Terraform state" command to manage Terraform state files.
The "Terraform state" command provides various subcommands to manage Terraform state files. It allows you to inspect, modify, and perform operations on the Terraform state. Common subcommands include "list" to list resources in the state, "mv" to move resources between states, and "rm" to remove resources from the state.
34. Explain the concept of remote state locking in Terraform and its importance in team collaboration.
Remote state locking in Terraform prevents concurrent modifications to the same state file by multiple users. When a user runs a Terraform command that modifies the state, the lock is acquired to prevent conflicts.
This ensures consistency and prevents data corruption in team-based workflows, where multiple users might be working on the same infrastructure.
35. How can you manage infrastructure secrets securely in Terraform, such as API keys or passwords?
To manage infrastructure secrets securely in Terraform, you can use environment variables or external systems like HashiCorp Vault. Storing sensitive data directly in Terraform configuration files is discouraged. Instead, you can define variables for secret values and populate them from external sources at runtime, ensuring confidentiality and separation of secrets from the configuration.
Wrapping up
Remember that knowing Terraform's essential principles, such as state management, resource provisioning, and infrastructure maintenance, is critical to acing your interview. Additionally, keep up to speed on the latest Terraform features and practices to demonstrate your commitment to ongoing learning and growth.
If you're searching for a high-paying remote software development job, Turing is the place to be. You can get matched to Silicon Valley jobs from the comfort of your own home with Turing, so if you believe you have what it takes to join the top development teams, sign up now.
If you are a hiring manager seeking top Terraform developers from across the world, Turing can help you find them in a matter of seconds. Our powerful AI-powered vetting platform objectively evaluates developers' hard and soft skills which boosts the strength of your business.
Hire Silicon Valley-caliber Terraform developers at half the cost
Turing helps companies match with top quality remote JavaScript developers from across the world in a matter of days. Scale your engineering team with pre-vetted JavaScript developers at the push of a buttton.
Tired of interviewing candidates to find the best developers?
Hire top vetted developers within 4 days.
Leading enterprises, startups, and more have trusted Turing

Check out more interview questions
Hire remote developers
Tell us the skills you need and we'll find the best developer for you in days, not weeks.